As supply chains have become more digitized and interconnected, they have also become more vulnerable to a range of cyber threats. These threats not only pose risks to the direct operations of companies but also to the extensive network of suppliers, providers, vendors,[1] and customers that constitute the supply chain ecosystem.
The transition of supply chains into the digital realm has undoubtedly introduced remarkable efficiencies and innovations. Yet, this same transformation has laid bare the cyber vulnerabilities inherent in these complex networks which has made supply chains – and the organizations involved in them – highly susceptible to cyberattacks, such as phishing, ransomware, malware, and data breaches, which can result in compromised sensitive data, financial loss, disruptions in services or operations, reputational harm, regulatory non-compliance, the endangerment to human life and safety, among other harms.
Supply Chain Cyberattacks By the Numbers:
- The number of organizations impacted by supply chain attacks has surged by more than 2,600% since 2018, with victims increasing 15% (to more than 54 million) in 2023 alone.
- Supply chain-related disruptions that occurred in 2023 led to an average $82 million in annual losses per organization in key industries, including financial services, aerospace, defense, health care, and energy.
- Gartner – the world’s leading research and advisory company – predicts that by 2025, 45% of organizations worldwide will have experienced attacks on their software supply chains – a three-fold increase from 2021.
This trend is unlikely to slow down any time soon, as attackers are continuing to refine their techniques and exploit weaknesses in the interconnected ecosystem of third-party vendors and software. Thus, more than ever before, it is crucial to recognize that supply chain vulnerabilities are now intricately woven into the fabric of cyber threats, marking a significant shift in how organizations across all industries alike approach the security of the interconnected networks. The growing interconnectedness of the global economy and the increasing number of cyber threats make it essential for organizations to assess and manage the risks posed by their supply chain partners.
In this article, we discuss the characteristics of supply chain cyberattacks, highlight recent high-profile incidents, and provide recommendations for mitigating the risks associated with them.
Understanding Supply Chain Cyberattacks
How They Work
A supply chain cyberattack takes advantage of trust relationships between different organizations. All organizations have a level of implicit trust in other companies as they install and use the company’s software within their networks or work with them as a vendors. Hackers often opt for the path of least resistance, targeting the weakest link in a chain of trust, due to their ability to infiltrate multiple organizations through a single point of compromise.
Even if your organization is well-defended and has a strong cybersecurity program in place, if one of your trusted vendors is not secure, attackers will target that vendor to bypass whatever security is in place in the vendor’s organization, such as by launching phishing schemes or social engineering attacks to compromise the credentials of a vendor’s employee.
Once the attackers gain a foothold within a vendor’s system, they explore and exploit vulnerabilities to move laterally across the network. For example, they may exploit unpatched software vulnerabilities, weak access controls, or misconfigured systems to escalate their privileges and further deepen their penetration to use it as a launchpad to deploy malware or malicious code or otherwise gain access to the networks of the primary target organizations. By exploiting vulnerabilities such as these in the supply chain, attackers can have greater impact and gain access to networks that are otherwise difficult to attack directly.
This aspect underscores the global scope of threats linked to supply chain cyberattacks. Hackers can intentionally or unintentionally gain control over any organization’s infrastructure, even if it has not been directly targeted. Also, it is not just immediate suppliers that organizations must worry about; the risks could run much deeper into the supply chain with third- and fourth-party suppliers, as the impact of a single supplier being disrupted can affect multiple parties down the chain. These include risks from compromised software or hardware purchased from suppliers, poor information security practices by lower-tier suppliers, software security vulnerabilities in supply chain management or supplier systems, and counterfeit hardware or hardware with embedded malware, among others.
Types of Supply Chain Cyberattacks
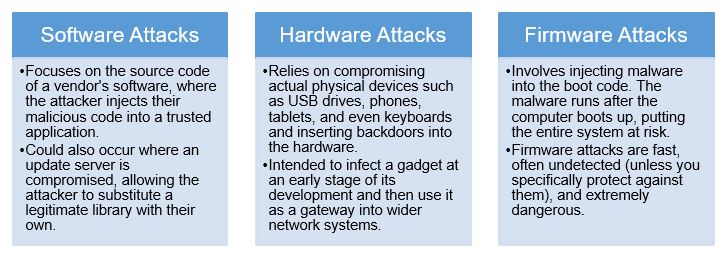
There are various forms of supply chain attacks, but three principal and most frequent ones stand out:
Recent High-Profile Case Studies
Over the last few years, several high-profile cybersecurity incidents have highlighted the growing threat to supply chains. These include:
- MOVEit (2023): MOVEit is a popular file transfer software that helps thousands of organizations around the world transfer large amounts of often sensitive files and data over the internet. In May 2023, a ransomware and extortion group called Cl0p gained access to data in corporate and institutional networks around the world by exploiting a zero-day vulnerability in the MOVEit software that allowed hackers to extract sensitive files from thousands of organizations that rely on this software, many of whom were third- and fourth-party vendors, suppliers, and contractors. As of October 2023, the MOVEit hack has reportedly affected at least 2,300 known public and private entities and more than 65 million individuals, for a global cost of more than $10 billion.
- Kaseya (2021): Attackers compromised this software solution used by managed service providers (MSPs), infecting it with REvil ransomware, which was then deployed together with an update of the software. The ransomware spread to thousands of customer environments, allowing attackers to extort $70 million from MSPs and their customers.
- SolarWinds (2020): This sophisticated cyber espionage campaign targeted the Orion software by SolarWinds, a popular IT management tool. By inserting malicious code into the software’s updates, attackers were able to infiltrate the networks of up to 18,000 SolarWinds customers, including key US government agencies and numerous Fortune 500 companies.
These case studies collectively underscore the critical importance of vigilance and robust security measures at all levels of the supply chain to mitigate the risks of such attacks.
Best Practices for Mitigating Cyber Risks Across Your Supply Chain
When your supply chain is only as strong as its weakest link, it is imperative for organizations to adapt by proactively managing and preparing for supply chain risks and cyber-related disruptions rather than merely reacting to problems as they occur. Here are some key best practices for organizations to consider implementing for effectively managing cyber risks impacting their supply chains:
- Risk Management Framework. Implement a comprehensive risk management framework that integrates Cyber Supply Chain Risk Management (C-SCRM) principles. C-SCRM is a systematic process for managing exposure to cybersecurity risk throughout supply chains and developing appropriate response strategies, policies, processes, and procedures. The National Institute of Standards and Technologies (“NIST”) Cybersecurity Framework (CSF) 2.0 provides a structured approach to managing cyber risks and can serve as a foundation for organizations of all sizes and sectors to develop their risk management strategies. CSF 2.0 also includes additional C-SCRM outcomes to help organizations address these risks. The subcategories within the CSF C-SCRM Category [GV.SC] serve as a bridge, linking cybersecurity-focused outcomes with broader C-SCRM objectives. For in-depth information on C-SCRM, please refer to NIST’s Special Publication (SP) 800-161r1, Cybersecurity Supply Chain Risk Management Practices for Systems and Organizations, SP 1305 (Initial Public Draft of a Quick Start Guide on How Organizations Can Utilize CSF 2.0 to Improve Their C-SCRM Processes), and C-SCRM Factsheet.
- Vendor Due Diligence. Conduct thorough due diligence when selecting vendors, assessing their cybersecurity posture, incident response capabilities, resilience, and adherence to applicable industry standards, laws, and regulations in relation to data protection, privacy, and cybersecurity. This helps in identifying and mitigating potential risks associated with third-party vendors.
- Assessing Vendors. Regularly carry out security assessments and audits of existing vendors to evaluate the effectiveness of cybersecurity controls and practices and to ensure compliance with relevant security standards and other applicable legal and contractual requirements throughout the supply chain lifecycle. It is also recommended that you implement C-SCRM practices to identify and mitigate supply chain risks associated with third-party providers.
- Vendor Contracts. Ensure there are robust cybersecurity requirements in every RFP and contract with a key supply chain provider that cover or address (at a minimum) resiliency of the providers’ own systems, regular training of personnel, prompt notice of a data breach, thorough cooperation, periodic audits, subcontracting, and other related measures necessary for compliance with applicable laws and industry standards, as well as clearly defined responsibilities and liability allocation with vendors. Companies should also regularly review and update existing vendor contracts to ensure that sufficient cybersecurity requirements are in place and seek addenda where there are not.
- Continuous Monitoring and Detection. Implement continuous monitoring and detection mechanisms to identify and respond to cyber threats in real-time. For example, organizations should consider utilizing threat intelligence feeds, security information and event management (SIEM) systems, and intrusion detection/prevention systems to monitor for suspicious activities and anomalies involving systems and/or software used within your supply chain.
- Education and Awareness. Provide regular cybersecurity awareness training to employees, suppliers, and stakeholders to (i) educate them about the importance of common cyber threats and best practices, (ii) promote awareness about C-SCRM principles and the importance of supply chain security in mitigating cyber risks, and (iii) help them recognize and encourage them to report potential cyber threats.
- Collaboration and Information Sharing. Foster collaboration and information sharing among supply chain partners to address common security challenges and share threat intelligence, best practices, and lessons learned.
- Secure Access Controls and Encryption Measures. Implement robust data encryption measures and access controls to protect sensitive information shared within the supply chain. Encrypting data both at rest and in transit helps in safeguarding it from unauthorized access or interception. Access controls (e.g., multi-factor authentication, role-based access controls, least privilege principles, etc.) help limit access to critical assets and systems by third-party providers.
- Incident Response and Business Continuity Plans. Develop or update existing incident response plans to include processes for responding to cyber incidents involving and originating from key third-party supply chain providers (and with relevant C-SCRM practices baked in to address supply chain-specific threats and vulnerabilities). In addition, it would be prudent to develop and regularly test business continuity and disaster recovery plans to ensure continuity of operations in the event of a supply chain cyberattack.
- Patch Management. Keep all software, including operating systems and applications, up to date with the latest security patches. Regular updates ensure vulnerabilities are promptly addressed.
Looking Ahead
The rising tide of supply chain disruptions caused by cybersecurity incidents demands a proactive response from businesses. Ignoring supplier risk management exposes companies to significant financial losses and reputational damage, and also can result in extreme harm to society. While cyber threats are inevitable, businesses can substantially minimize their impact by implementing a strong supplier risk management framework together with more robust security measures. In doing so, organizations can also better protect their valuable assets, reputation, and stakeholder relationships.
1 The terms suppliers, vendors, and providers are referred to interchangeably throughout this article.




 />i
/>i

